Our Services
We provide end-to-end support for organizations to achieve compliance with the National Cybersecurity Controls, ensuring readiness for regulatory audits and improving overall cybersecurity posture.
Cybersecurity Gap Assessment
We evaluate your current security posture against required frameworks and identify gaps with clear remediation priorities.


Cybersecurity Compliance Implementation
We support organizations in implementing cybersecurity frameworks aligned with national and international standards, ensuring structured and measurable compliance.


Policy Development
We design and develop comprehensive cybersecurity policies aligned with governance requirements and operational realities.


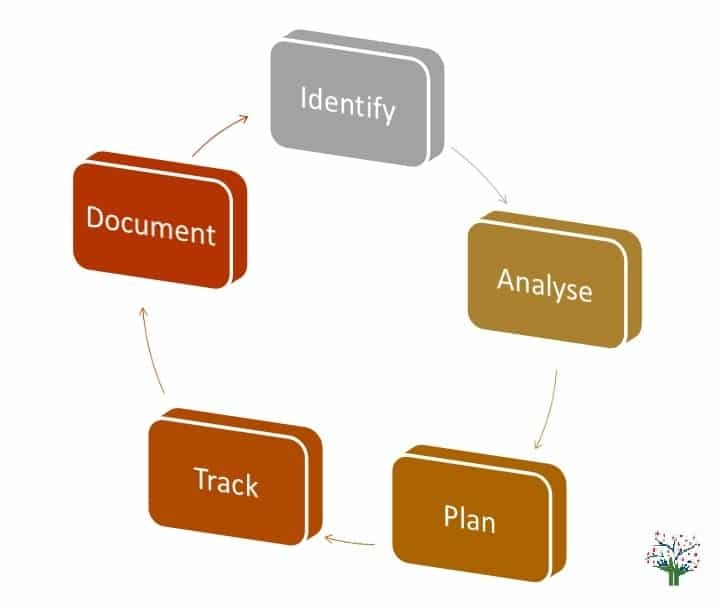
Risk Assessment
We identify, analyze, and prioritize cybersecurity risks, translating technical findings into business impact and decision-ready insights.